Threat intelligence strengthens security programs by bringing foresight and awareness to existing functions such as security operations centers (SOCs) and asset management. However, not all threat intelligence is created equal. Tactical threat intelligence, on the other hand, consists of activities such as ingesting indicators of compromise (IOCs) to create detection or blocking rules within the tool. Then there’s the other side, strategic threat intelligence, which is the focus of this analysis.
Analyze strategic threat intelligence
Strategic threat intelligence sees the big picture. This includes a broader, longer-term view of the relationship between cyber threats and the investments in the programs you are working on. This includes threat landscape analysis, industry and sector-specific analysis, and geopolitical threat analysis.
All of this is a signal (or input to a process), but having a large amount of data does not directly provide insight into how it impacts an organization and its plans. As a team, you must: think critically Think about these in the context of your organization’s strategy.
One approach to supporting such critical thinking in this strategic threat intelligence context is to adopt a structured analytical framework that: Analysis of competing hypotheses (ACH). ACH encourages participants to simultaneously investigate multiple hypotheses, gather evidence, and evaluate the relative likelihood of each before reaching a conclusion. By using critical thinking frameworks like ACH, teams can minimize the influence of cognitive biases in this critical process and make informed decisions that contribute to more resilient strategies. I can.
The next section of this analysis details some specific questions you can incorporate into your planning process. The ACH framework helps teams think creatively and objectively about possibilities (or hypotheses). As you gain confidence in certain things, you can move on to more specific plans.

Strategic planning questions
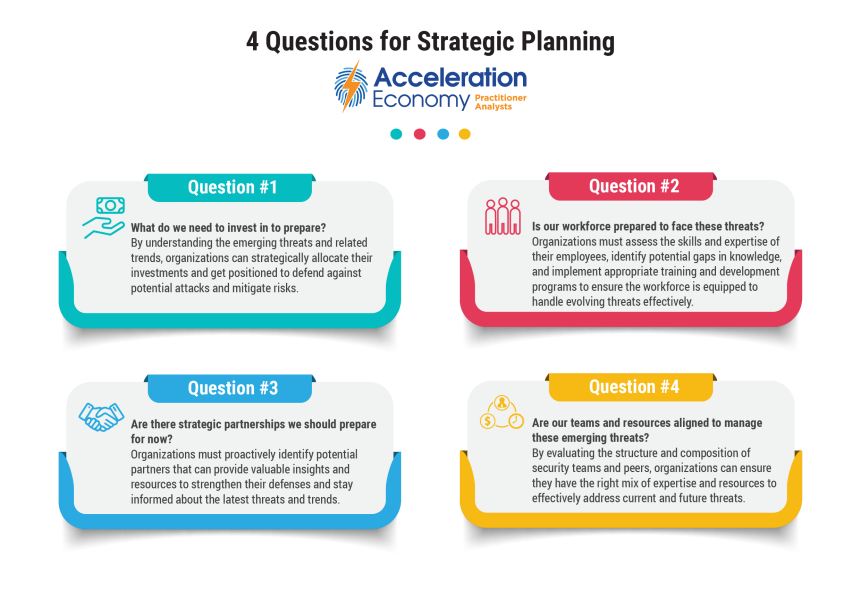
The following questions can be included in the strategic planning process along with collected threat intelligence data, reports, and thematic output.
1. What should I invest in to prepare?
Strategic planning is about preparing for the future based on your goals and current situation. This, along with an understanding of emerging threats and trends, enables organizations to strategically allocate investments, proactively defend against potential attacks, and be well prepared to mitigate risk. I can. For example, organizations that have not invested in supply chain visibility technologies may be unprepared for supply chain tampering attacks such as Log4Shell.
2. Are our employees prepared to face these threats?
This question highlights the importance of human capital in cybersecurity. This is an appropriate training and development program that allows organizations to assess the skills and expertise of their employees, identify potential gaps in knowledge, and enable employees to effectively deal with evolving cyber threats. We encourage you to implement the following. This may mean investing in training, culture change, or something else entirely. With the current explosion of artificial intelligence (AI) tools on the market, a workforce that is unable to take advantage of such tools and quickly adapt to the complexities of both the rapidly changing market and threat landscape. may be less flexible and susceptible. Attacks by agile attackers.
3. Is there a strategic partnership you should start preparing for now?
This question is important because collaboration and information sharing has strategic value in strengthening cybersecurity. This question will help your organization identify potential partners (peers, information sharing groups, cybersecurity vendors) who can provide valuable insights and resources to strengthen your defenses and stay informed about the latest threats and trends. will be proactively identified. This may look like a critical assessment of employee skills and headcount, as well as an examination of relationships with outsourcing vendors, such as managed security service providers (MSSPs), to address key functional areas.
Four. Are our teams and resources aligned to address these emerging threats?
Coordination of resources is the basis of effective strategic planning. This question requires organizations to evaluate the structure and composition of their security team, along with other teams, to ensure the right mix of expertise and resources to effectively address current and future threats. We also encourage organizations to evaluate their internal communication and collaboration mechanisms to facilitate a unified and coordinated response to emerging cyber threats. In this case, an overly hierarchical organization may spend more time dealing with ownership issues and change management than adapting quickly when something significant happens.
conclusion
Threat intelligence is not just about IOCs, daily work against active threats, and environment updates. There is real strategic value in examining how threats evolve and how this relates to strategic planning. Cybersecurity cannot be separated from an organization’s strategy. This is a great opportunity to integrate and make it happen.
This article has been updated since it was first published April 27, 2023.
Want more cybersecurity insights? Visit our Cybersecurity Channel.