Ron Amadeo
It turns out that companies that block the media’s security questions aren’t actually good at security. Last Tuesday, Nothing Chats, a chat app from Android maker Nothing and startup app company Sunbird, brazenly claimed it could hack Apple’s iMessage protocol to give Android users blue bubbles. We immediately flagged Sunbird as a company that had been making empty promises for almost a year and appeared to be negligent about security. Anyway, the app was released on Friday, but was quickly shattered by the internet due to numerous security issues. On Saturday morning, it took less than 24 hours for the Nothing app to be removed from the Play Store. His Sunbird app, which was just a reskin of Nothing Chat, was also “suspended.”
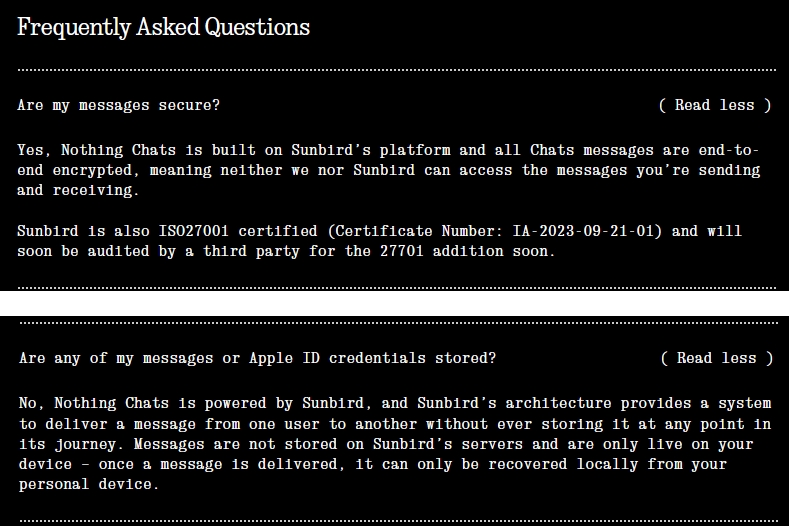
The app’s initial sales pitch (that it lets you log in to iMessage on Android by handing in your Apple username and password) was a big security red flag, and Sunbird is confident it has an ultra-secure infrastructure in place to avoid disaster. It was meant to be necessary. Instead, it turns out that this app is not as secure as it could be. Here is Nothing’s statement:
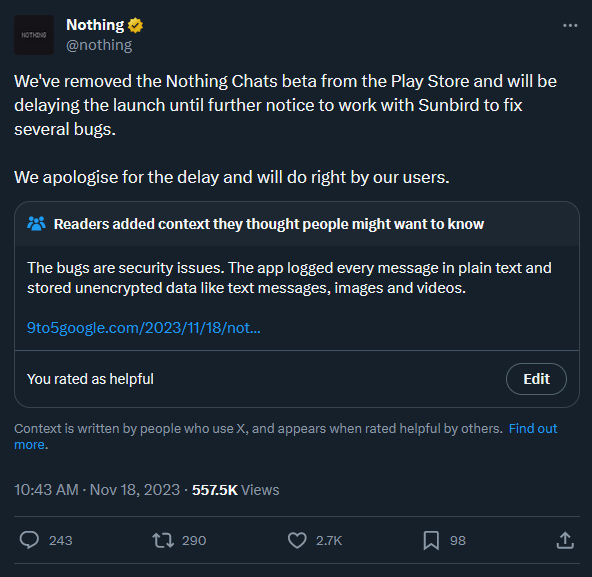
Nothing Chat posting has been closed.
How serious is the security issue? Both 9to5Google and Text.com (The owner is automatic, the company behind WordPress, has revealed shockingly bad security practices. Not only was the app not end-to-end encrypted, as Nothing and Sunbird have repeatedly claimed, but Sunbird actually logged and stored messages in clear text in both error reporting software. I did. guard and In the Firebase store. Because the authentication token is sent over unencrypted HTTP, it can be intercepted and used to read messages.
Text.com’s research uncovered numerous vulnerabilities. The blog says, “Once messages or attachments are received by a user, they are not encrypted server-side until the client sends an authorization request to remove them from the database. This is because an attacker could use Firebase Realtime It means you have subscribed to the DB.” You can access your messages at any time, before or at the moment the user reads them. ” Text.com was able to intercept authentication tokens sent over unencrypted HTTP and subscribe to changes occurring in the database. This meant live updates of “receiving messages, sending messages, changing accounts, etc.” not only from yourself but also from other users.
Released by Text.com proof of concept This app will supposedly be able to retrieve end-to-end encrypted messages from Sunbird’s servers. Batuhan Isos, a product engineer at Text.com, also released a tool to remove some data from Sunbird’s servers. Içöz recommends that Sunbird/Nothing Chat users change their Apple IDs now, cancel their Sunbird sessions, and “assume your data has already been compromised.”
9to5Google Dylan Roussel investigated the app and found that in addition to all public text data, “all documents (images, videos, audio, PDFs, vCards…) sent through Nothing Chat and Sunbird are publicly available.” got it. Roussel discovered that 630,000 media files are currently stored on Sunbird, some of which appear to be accessible. Sunbird’s app offers users to transfer her vCard, a virtual business card packed with contact data, and Roussel says it has access to the personal information of more than 2,300 users. Roussel calls the entire fiasco “probably the biggest ‘privacy nightmare’ I’ve seen from a cell phone manufacturer in years.”
Nothing is guaranteed to be secure as it is incredibly unremoved.
Despite being the cause of this catastrophe, Sunbird remained strangely silent during this chaos. The app’s X (formerly Twitter) page doesn’t yet say anything about the closure of Nothing Chats or Sunbird. This is probably for the best, as some of his Sunbird’s early responses to the security concerns raised on Friday don’t seem to come from a competent developer. Initially, the company defended its use Some web transactions use unencrypted HTTP, telling Text.com’s Bagaria:HTTP is only used as part of a one-time initial request from the app to notify the backend of future iMessage connection iterations via a standalone communication channel. Sunbird has focused on security from the beginning.Text.com’s investigation revealed that this is a “load-balanced Express server that does not implement SSL, so requests could easily be intercepted by an attacker.” This use of HTTP allowed Text.com to intercept the authentication token.
Modern security best practices never allow the use of unencrypted HTTP for internet transactions, and many platforms completely block plain text HTTP transmissions by default. Chrome displays a page-wide warning when attempting to access an HTTP page, and users must click through the warning message.android disable clear text Traffic is generated by default, so developers must turn on special flags to allow requests to pass. Projects like Let’s Encrypt have not only made using HTTPS easy and free; Easier You can encrypt everything so you don’t have to deal with all the security hurdles. These are the basics of his internet usage in 2023, and it’s shocking to see developers refute them. Especially if that developer wants to trust his Apple account. Unless this was some terrible mistake, Sunbird thought this was fine.
Never before has there been more hype than substance for Android manufacturers, and now we can add “negligence” to that list. The company took note of his Sunbird and changed the app skin, promotional website and YouTube videoand coordinated media releases. Popular YouTuber, without doing even the slightest bit of due diligence on Sunbird’s app or its security claims. I can’t believe that his two companies have made it this far. Launching Nothing Chats required systemic security failures across the two companies.
Nothing claims that the app will return once the app and Sunbird “fix some bugs.” If your entire app is built with seemingly no security in mind, I doubt you can patch it in a week or two. Even if Nothing Chats is back on the Play Store, will anyone trust it enough to enter their credentials?