MrAnon Stealer can steal data and collect information from cryptocurrency wallets, browsers, messaging apps, and VPN clients.
Cybersecurity researchers at FortiGuard Labs have uncovered a new email phishing campaign that leverages fake hotel reservations to lure unsuspecting victims. This phishing attack involves the deployment of a malicious PDF file that, when opened, triggers a series of events that lead to the activation of the MrAnon Stealer malware.
Rather than relying on complex technical details, attackers pose as hotel reservation companies and send phishing emails with the subject line “December Availability Inquiry.” The body of the email contains fabricated holiday booking details, and the malicious PDF file has a hidden downloader link.
After further investigation, FortiGuard Labs cybersecurity experts discovered a multi-step process involving a .NET executable, a PowerShell script, and a deceptive Windows Forms presentation. Attackers posing as hotel reservation companies successfully bypass these stages by using tactics such as fake error messages to hide successful execution of the malware.
MrAnon Stealer, a Python-based information stealer, works discreetly and compresses activity with cx-Freeze to evade detection mechanisms. The malware performs elaborate processes such as capturing screenshots, harvesting IP addresses, and stealing sensitive data from various applications.
Attackers are sophisticated in terminating certain processes on the victim’s system and masquerading as legitimate connections to obtain IP addresses, country names, and country codes. Stolen data such as credentials, system information, and browser sessions are compressed, password-protected, and uploaded to public file-sharing websites.
According to FortiGuard Labs blog post, MrAnon Stealer can collect information from cryptocurrency wallets, browsers, and messaging apps such as Discord, Discord Canary, Element, Signal, and Telegram Desktop. Additionally, it targets VPN clients such as NordVPN, ProtonVPN, and OpenVPN Connect.
As for its command and control. The attacker uses her Telegram channel as a communication medium. The stolen data, system information, and download links are sent to the attacker’s girlfriend Telegram channel using the bot token.
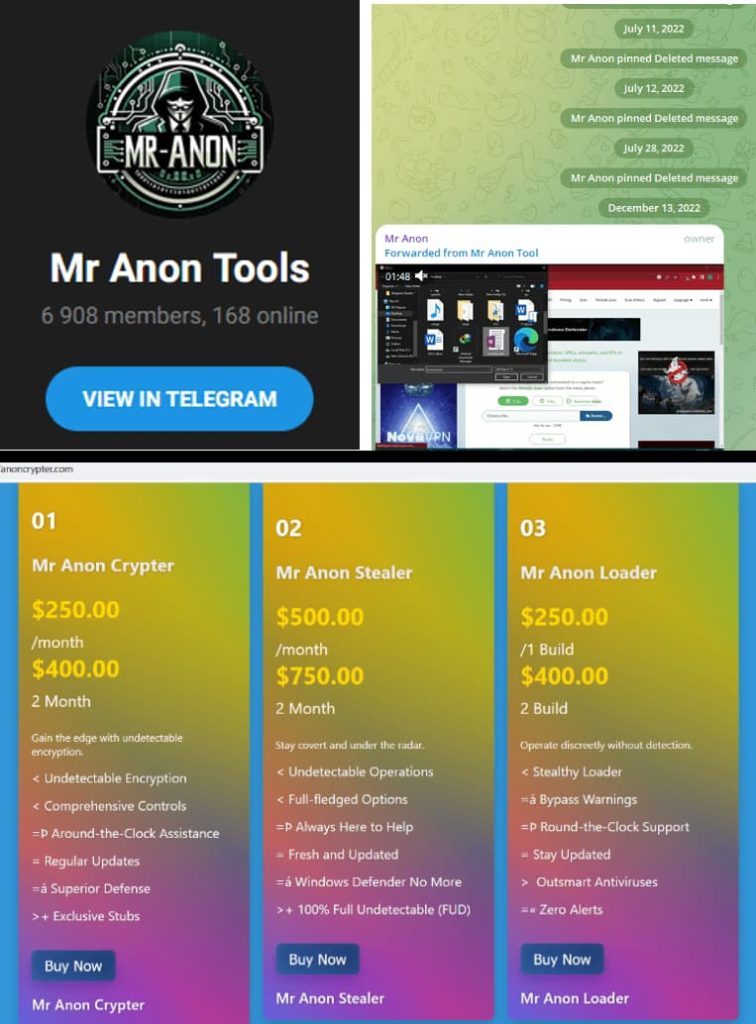
The campaign was active and active in November 2023 and primarily targeted Germany, as evidenced by the spike in queries for the downloader URL during that period. The cybercriminal behind this operation demonstrated a strategic approach, moving from his Cstealer in July and August to his more powerful MrAnon Stealer in October and November.
If you’re online, you’re vulnerable. Therefore, users are advised to be careful while dealing with unexpected emails, especially those with suspicious attachments. Prudence and common sense are key to thwarting cybercriminals’ attempts to exploit human vulnerabilities and compromise online security.
Related article
- Booking.com scam targeting guests using Vidar Infostealer
- Silent Ransom Group uses callback phishing to hack networks
- USPS delivery phishing scam exploits SaaS providers to steal data
- Iran’s Muddy Water Group attacks Israelis with spear phishing of fake notes
- LinkedIn phishing scam uses Smart Link to steal Microsoft accounts









