There has been a significant increase in zero-day and remote code execution in recent attacks. Kratikal observed that the attackers were particularly focused on his web apps, IoT, and open source tools. This blog describes a recently discovered remote code execution attack on Apache Struts2. Apache Struts helps a developer to create his web applications in Java. It also helps developers maintain and secure their web applications.
For developers and security experts, December didn’t start out on a happy note, but rather with a menacing shock. On December 7th, the Apache Software Foundation disclosed a critical vulnerability in Apache Struts2. CVE-2023-50164. The flaw is embedded in the core of the popular open source web framework and has an astonishingly high Common Vulnerability Scoring System (CVSS) score of 9.8, firmly placing it in the “severe” category. Classified.So what exactly can you do? CVE-2023-50164 Very dangerous. How do I fix this vulnerable hole in my web application?
Why is it important? Understanding vulnerabilities
At its core, CVE-2023-50164 Exploits a flaw in Struts2’s file upload logic. Imagine this. An attacker creates a carefully crafted file upload request and manipulates certain parameters. Instead of uploading a benign document, this request allows the attacker to traverse the server’s file system, potentially reaching sensitive data or embedding malicious files. But the real nightmare unfolds when you realize that this malicious file can be executed. Yes, that’s right. Remote code execution (RCE) is being considered.
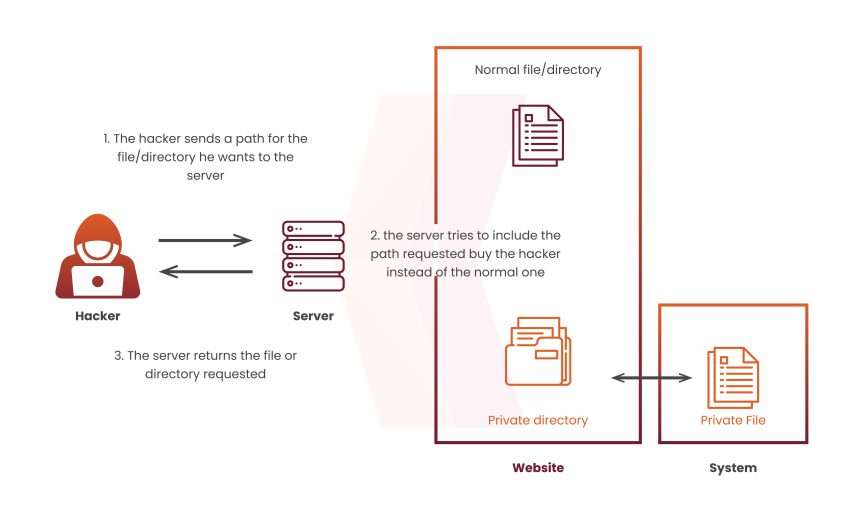
Parameter pollution and path traversal bugs
This bug causes path traversal to access files outside of the root directory. This vulnerability also causes parameter pollution if the attack modifies the initial parameters and adds additional lowercase parameters. This allows an internal filename variable to be overridden and the system exploited to allow the attacker to execute remote code.
RCE is a major concern when it comes to secure systems. If exploited, this vulnerability could allow a hacker to take over the server. User passwords, financial details, sabotage, and more can be compromised. The impact can be severe, damaging people, businesses, and critical resources alike.
Threat scope: Who is vulnerable?
The worst part? This vulnerability affects many applications developed with Struts2. All versions 2.5.0 through 2.5.32 and 6.0.0 through 6.3.0 are vulnerable. Struts2 has a wide user base, powering enterprise applications, government websites, and private companies. This means there is a high probability of attack. CVE-2023-50164 It is a serious threat to organizations around the world.
Combating remote code execution: Immediate action required
So what should organizations do to patch immediately? Apache has released patched versions for all affected Struts2 versions. Upgrading to Struts 2.5.33 or Struts 6.3.0.2 or later is the ultimate and most effective solution. Don’t delay. Delaying can lead to serious consequences.
However, just applying a patch won’t help. Here are some additional tips to help prevent these critical vulnerabilities.
Scan your environment. Perform a thorough scan of your system to identify applications using vulnerable versions of Struts2. Prioritize patching these applications first.
Monitor for suspicious activity: Implement security monitoring tools and SIEM solutions to detect suspicious activity that may indicate an exploit attempt.
Raise awareness: Train your employees and developers about vulnerabilities and the importance of patching. Encourage a culture of security awareness to prevent future exploits.
Post-patch tasks: Building defense in depth
While patching is important, it’s important to remember that it’s only one piece of the puzzle. A layered security approach is key to truly mitigating the risks posed by vulnerabilities such as: CVE-2023-50164. Here are some layers you can add to your defense.
Implement input validation. Validate all user input to prevent malicious code from being uploaded or executed.
Restrict file extensions: Limit the types of files that can be uploaded to only those needed by your application.
Schedule a free consultation with a cybersecurity expert
Controlling user access: Make sure you implement strict user access controls to ensure that only privileged users can access sensitive data.
Keep your software updated: This is a basic that everyone must follow, whether they work in the field or not. cyber security or not.
conclusion
CVE-2023-50164 This is a critical vulnerability with potentially devastating consequences. However, by acting quickly, increasing awareness, and implementing a multi-layered security approach, you can reduce risk and prevent your systems from falling victim to this fundamental flaw.
It is essential to address serious vulnerabilities CVE-2023-50164 With Apache Struts2. Patching is important, but a comprehensive defense plan is critical. Upgrade to Struts 2.5.33 or Struts 6.3.0.2, run system scans, keep an eye out for unusual activity, and spread awareness by your organization.
Cratical, CERT-In Qualified Auditor is an essential component in the fight against cyber threats. Governance, risk and compliance Identify, prevent, and minimize vulnerabilities. Cratical We help businesses defend against evolving threats by providing proactive protection, security training, and advanced scanning tools. Remember that security is an ongoing effort, not a one-time solution. Patching, cyber vigilance, and proactive defense are our weapons against evolving cyber threats. Use it wisely to make your digital world safer.
post Impact of Apache Struts2 code execution vulnerability It first appeared Cratical’s blog.
*** This is a syndicated blog from the Security Bloggers Network. Cratical’s blog The author is Ridika Grover. See the original post here: https://kratikal.com/blog/impact-of-apache-struts2-code-execution-vulnerability/