Thousands of WordPress sites using vulnerable versions of the Popup Builder plugin were compromised by malware called “Popup Builder.” baradain injector.
The campaign, first documented by Doctor Web in January 2023, comes in a series of regular waves of attacks, weaponizing security flawed WordPress plugins to lure visitors to infected sites. Injects backdoors, lottery winning scams, and push notification scams designed to redirect to fake tech support pages. .
Subsequent discoveries excavated by Sucuri revealed the massive scale of this operation. The operation has been active since his 2017 and is said to have compromised over 1 million sites since then.
Website security company owned by GoDaddy. detected With the latest activity of Balada injector on December 13, 2023, 7,100+ sites.
These attacks are based on the popup builder (CVE-2023-6000CVSS score: 8.8) – Plugin with Over 200,000 active installations – It was published by WPScan the previous day. This issue was resolved in version 4.2.3.
“Successfully exploiting this vulnerability could allow the attacker to perform any action that a targeted logged-in administrator could perform on a targeted site, including installing arbitrary plugins or creating a new unauthorized administrator user. “It’s possible,” said WPScan researcher Marc Montpas. Said.
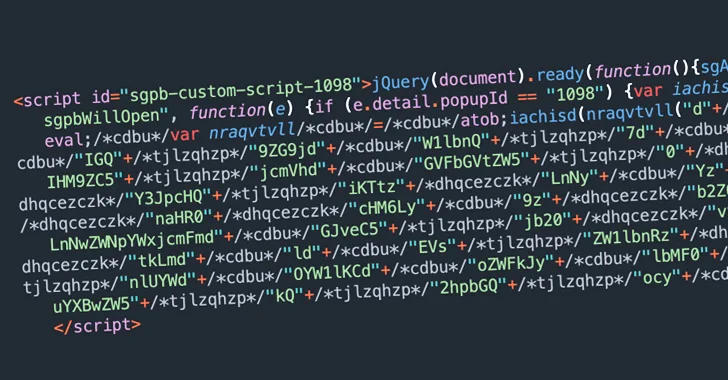
The ultimate goal of this campaign is to inject a malicious JavaScript file hosted on specialcraftbox.[.]com and uses it to control the website and load additional JavaScript to facilitate malicious redirects.
Additionally, the attackers behind Balada Injector establish permanent control over compromised sites by uploading backdoors, adding malicious plugins, and creating rogue blog administrators. It is known that
This is often achieved by using JavaScript injection to specifically target logged in site administrators.
“The idea is that when a blog administrator logs into a website, their browser includes a cookie that allows them to perform all administrative tasks without having to authenticate on each new page.” Sucuri researcher Denis Sinegubko pointed this out last year.
“So if your browser loads a script that attempts to emulate administrator activity, it will be able to do almost anything you can do through the WordPress admin interface.”
The new wave is no exception, and once a logged-in administrator cookie is detected, it uses its elevated privileges to install a rogue backdoor plugin (“wp-felody.php” or “Wp Felody”). Activate and get the second plugin. -stage Payload from the aforementioned domain.
Another backdoor, the payload, is named “sasas” Directory where temporary files are savedthen executed and removed from disk.
“It checks up to three levels up from the current directory, looking for the current site’s root directory and other sites that may share the same server account,” Sinegubko said.
“It then modifies the wp-blog-header.php file in the root directory of the detected site to inject the same Balada JavaScript malware that was originally injected via the Popup Builder vulnerability.”