The scraped LinkedIn database was leaked in two parts. One part contained 5 million user records and the other part contained 35 million records.
The LinkedIn database containing the personal information of over 35 million users was leaked by hackers operating under the alias USDoD. The database was leaked on a notorious cybercrime and hacker platform. infringement forum.
It’s important to note that USDoD is the same hacker who broke into the FBI’s security platform InfraGard last year and leaked the personal information of 87,000 of its members.
In a post on the breach forum, the hacker confirmed that the latest LinkedIn database was obtained in the following manner: web scraping. Web scraping is an automated process utilized by software to extract data from websites, primarily to collect certain information from web pages.
The contents of the data are as follows. hackreadcomthe database mainly consists of information publicly available from: linkedin Profile including full name and profile bio. Note that while the database contains millions of email addresses, the leaked data does not include passwords.
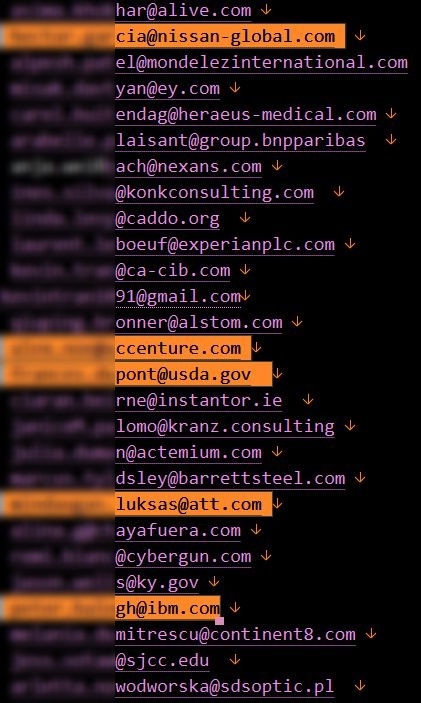
The screenshot below shows that the email addresses included in the compromise belong to US government officials and agencies. Additionally, email addresses from various government agencies around the world have also been identified.
The validity of LinkedIn data: real or fraudulent?
Troy Hunt on HaveIBeenPwned analyzed They extracted more than 5 million accounts from the database and concluded that the information was mixed from a variety of sources, including public LinkedIn profiles, fabricated email addresses, and other sources. Troy emphasizes that while some of the data may be anecdotal or partially fabricated, the people, companies, domains, and many of his email addresses are real.
“In conclusion, this corpus contains important components of legitimate data, so we loaded it into HIBP.“ Mr. Hunt explained. “However, it also contained a significant number of fabricated email addresses, so I flagged it as a spam list. This means that if you monitor a domain, its address will not affect the size of your paid subscription.“
However, this isn’t the first time LinkedIn’s decommissioned database has been leaked online. In April 2021, the attacker was selling his two scraped LinkedIn databases containing 500 million records and his 827 million records. In June 2021, hackers sold a discarded LinkedIn database containing data on 700 million users.
Related article
- LinkedIn phishing attack in which hackers pose as Israelis
- Twitter scraping breach: 209 million accounts exposed on hacker forum
- API Exploitation: Hackers exposed the email addresses and names of 2.6 million Duolingo users
- Meta fined 265 million euros over EU Facebook data scraping scandal
- Data scraping company leaks 235 million user data from Instagram, TikTok, and YouTube









