The scraped Chess.com data was leaked on a breach forum on November 8, 2023 by a threat actor operating under the alias “DrOne.”
An attacker operating under the alias “DrOne” has claimed responsibility for leaking Chess.com’s scraped database containing the personal data of over 800,000 registered users.
Chess.com is a very popular online platform and social networking website for chess enthusiasts. As of 2023, the platform boasts over 150 million registered users, and the leaked records show that it only represents about 0.533% of its total user base.
This database was published on November 8, 2023 on Breach Forums, a well-known platform for hacker and cybercriminal activities. Interestingly, this forum recently witnessed another attacker leaking the following information: Scraping the database from LinkedIn Just a few days ago, it contained information from 25 million users.
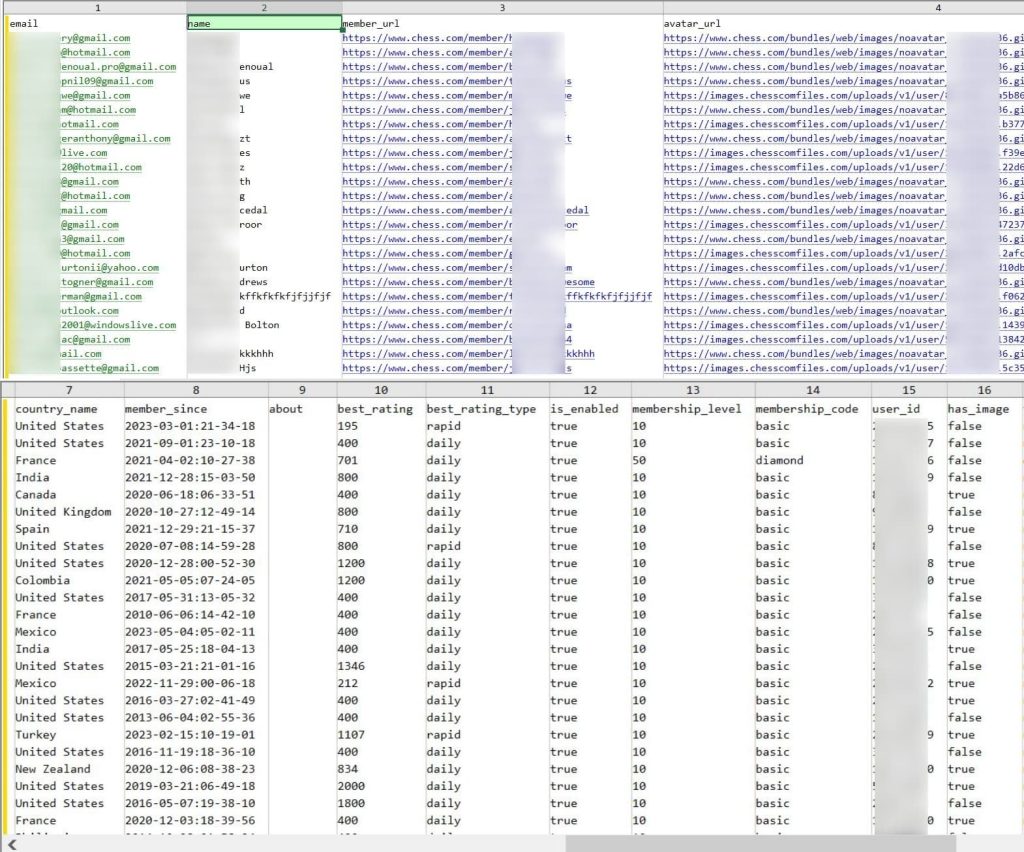
leaked data
After a comprehensive scan of the Chess.com database by Hackread.com, analysis confirmed that personal data from 828,327 registered users had been compromised. The leaked information includes:
- full name
- username
- Profile link
- email address
- User country of origin
- Avatar URL (including profile photo)
- Universally Unique Identifier (UUID) and User ID
- Registration date (latest sign-up is September 2023)
When combined, leaked information can become a gold mine for cybercriminals. This data can be used for identity theft, phishing, social engineering attacks, or to cross-reference previously compromised login credentials to retrieve passwords.
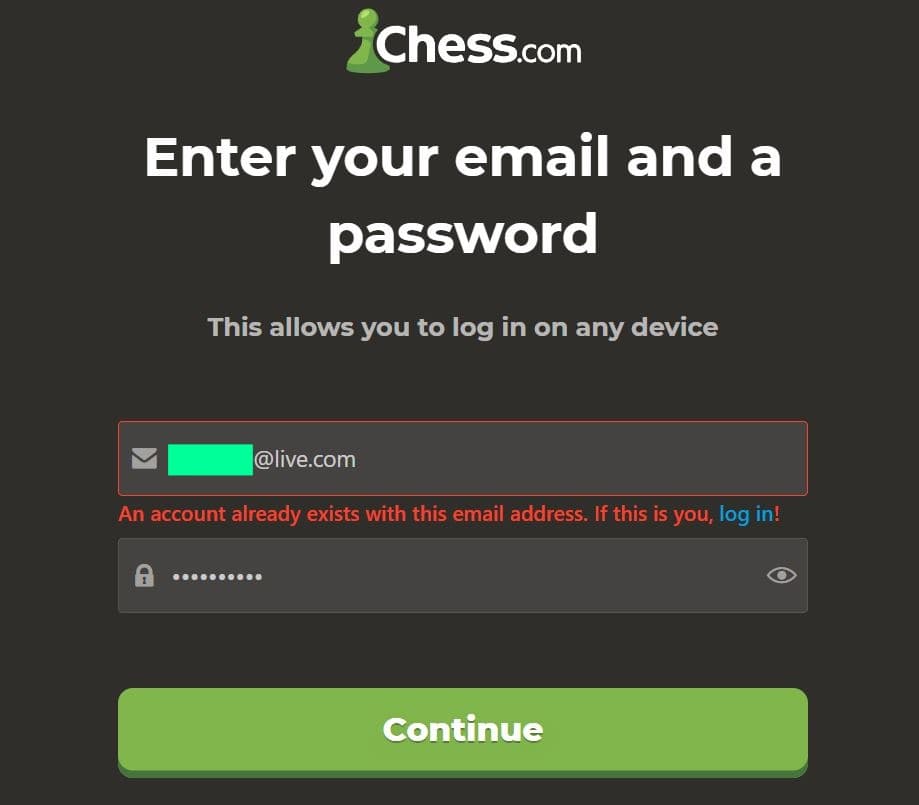
Fortunately, passwords are not included in the leaked data. However, when Hackread.com tried to sign up using the leaked email addresses, a message appeared on almost every email address used. “An account with this email address already exists.” This suggests that the leaked database contains valid and active email addresses associated with existing Chess.com accounts.
Web scraping is difficult to avoid/block
Web scraping or data scraping is an automated process utilized by software to extract data from websites, primarily to collect certain information from web pages. Since Chess.com is a large website, it is almost impossible to block this process.
Large websites use various methods to prevent scraping, such as rate limiting and captcha challenges. However, scrapers are constantly developing new techniques to circumvent these measures, and some scrapers may collect data for research purposes, such as studying social networks or developing machine learning models.
Chess.com and Cybersecurity
This isn’t the first time Chess.com has made headlines for cybersecurity-related issues. February 2021, renowned ethical hacker Sam Curry discovered and reported a critical vulnerability within the platform. This flaw could have allowed researchers to access any account on the site, including administrator accounts.
This new breach poses a significant threat to Chess.com users and could facilitate a variety of scams, including identity theft and phishing. If you are a Chess.com user, we strongly recommend that you change your password not only on the platform, but also on any other online accounts where the same password is used.
Cybercriminals may introduce phishing tactics, sends emails containing links to malicious websites that mimic Chess.com or other legitimate platforms. It is important that you do not click on such links. However, you can safely verify the actual URL by hovering over the link before clicking it.
Hackread.com notified Chess.com about the data breach. This article will be updated if we hear back from the companies.
Related article
- Hackers leak scraped data of 87,000 GETTR users
- Scraping data of 1.3 million Clubhouse users is published online
- Twitter scraping breach: 209 million accounts exposed on hacker forum
- API Exploitation: Hackers exposed the email addresses and names of 2.6 million Duolingo users
- Data scraping company leaks 235 million user data from Instagram, TikTok, and YouTube









