Iranian state-sponsored threat actor known as oil rig deployed three different downloader malware throughout 2022 to maintain persistent access to victim organizations located in Israel.
The three new downloaders have been named ODAgent, OilCheck, and OilBooster by Slovak cybersecurity company ESET. The attack also involved the use of an updated version of a known OilRig downloader called SampleCheck5000 (or SC5k).
“These lightweight downloaders […] It is known for using one of several canonical cloud service APIs. [command-and-control] “Communications and Data Exposure: Microsoft Graph OneDrive or Outlook API, and Microsoft Office Exchange Web Services (EWS) API” by security researchers Zuzana Hromcová and Adam Burgher. Said In a report shared with The Hacker News.
By using a well-known cloud service provider for command and control communications, the aim is to blend with real network traffic and hide the group’s attack infrastructure.
Targets of the campaign include organizations in the healthcare sector, manufacturing companies, and local governments. All victims are said to have been previously targeted by threat actors.
Defeat AI-powered threats with Zero Trust – Webinar for security professionals
In today’s world, traditional security measures are no longer the answer. The era of zero trust security has arrived. Protect your data like never before.
The exact initial access vector used to compromise the target is currently unknown, and it is unclear whether the attackers were able to maintain a foothold within the network to deploy these downloaders at various points in 2022. Unknown.
OilRig, also known as APT34, Crambus, Cobalt Gypsy, Hazel Sandstorm (formerly EUROPIUM), and Helix Kitten, is an Iranian cyberespionage group known to have been active since at least 2014 and has a wide range of malware at its disposal. is used to aim at the target. Middle Eastern entity.
This year alone, hacker groups have been observed leveraging new malware such as MrPerfectionManager, PowerExchange, Solar, Mango, and Menorah.
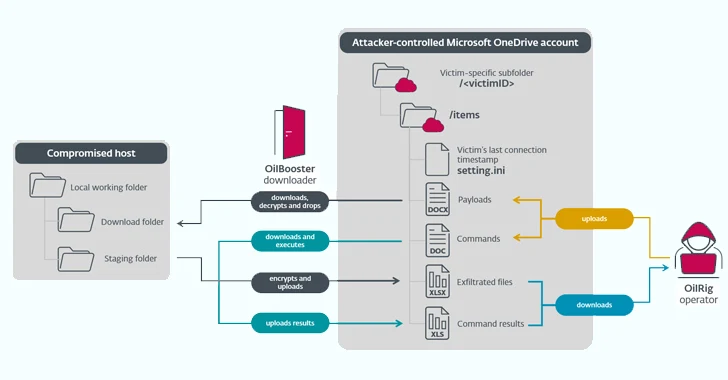
First detected in February 2022, ODAgent is a C#/.NET downloader that leverages the Microsoft OneDrive API for command-and-control (C2) communications, allowing attackers to download and execute payloads and exfiltrate staged files. I will make it possible.
SampleCheck5000, on the other hand, is designed to interact with a shared Microsoft Exchange email account and use the Office Exchange Web Services (EWS) API to download and run additional OilRig tools.
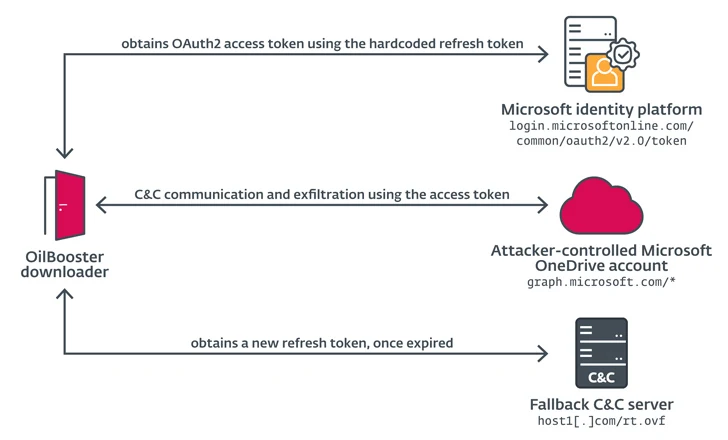
OilBooster, like ODAgent, uses the Microsoft OneDrive API for C2, while OilCheck employs the same technique as SampleCheck5000 to extract commands embedded in draft messages. However, instead of using the EWS API, it leverages the Microsoft Graph API for network communication.
OilBooster is also similar to OilCheck in that it uses the Microsoft Graph API to connect to Microsoft Office 365 accounts. The difference this time is that the API is used to interact with an attacker-controlled OneDrive account rather than an Outlook account in order to retrieve commands and payloads from victim-specific folders.
These tools share similarities with MrPerfectionManager and the PowerExchange backdoor in that they use email-based C2 protocols to steal data. However, in the latter case, the victim organization’s Exchange Server is used to send the attacker’s email message to her account.
“In each case, the downloader uses a shared (email or cloud storage) account operated by OilRig to exchange messages with the OilRig operator. Typically, the same account is shared by multiple victims.” explained the researchers.
“The downloader accesses this account to download commands and additional payloads staged by the operator, and to upload command output and staged files.”