Notably, the developers of the notorious Lumma information-stealing malware have already taken advantage of this exploit by employing advanced tactics such as token manipulation and encryption in targeted attacks.
CloudSEK’s threat research team has reported a critical exploit impacting Google services. This allows an attacker to perform an attack. Google cookies Provides continued access, ensuring continued access to Google services even after users reset their passwords. CloudSEK shared details of this exploit in a technical report.
On October 20, 2023, CloudSEK’s AI digital risk platform XVigil discovered on its Telegram channel that developer and threat actor PRISMA has released a zero-day solution that addresses issues with incoming sessions for Google accounts.
This solution provides session persistence, allowing an attacker to bypass security measures and generate cookies to gain unauthorized access even if the account password changes. The developer has expressed openness to possible cooperation and cooperation regarding this newly discovered exploit.
after that, Lumma Infostealer announced the integration of this feature with an advanced black-box approach on November 14, 2023. Rhadamanthys and WhiteSnake have also announced similar black-box approaches. Lumma updated the exploit to counter Google’s fraud detection measures on November 24, 2023. Other hackers such as Stealc, Meduza, RisePro, and Whitesnake have also implemented this feature. Hudson Rock posted a dark web video on December 27, 2023 demonstrating hackers exploiting his generated cookies.
CloudSEK Threat Researcher revealed An undocumented Google Oauth endpoint named “MultiLogin” is believed to be the root of the exploit. The endpoint responsible for regenerating cookies was revealed through the source code of her Chromium, an internal mechanism designed to synchronize Google accounts between services.
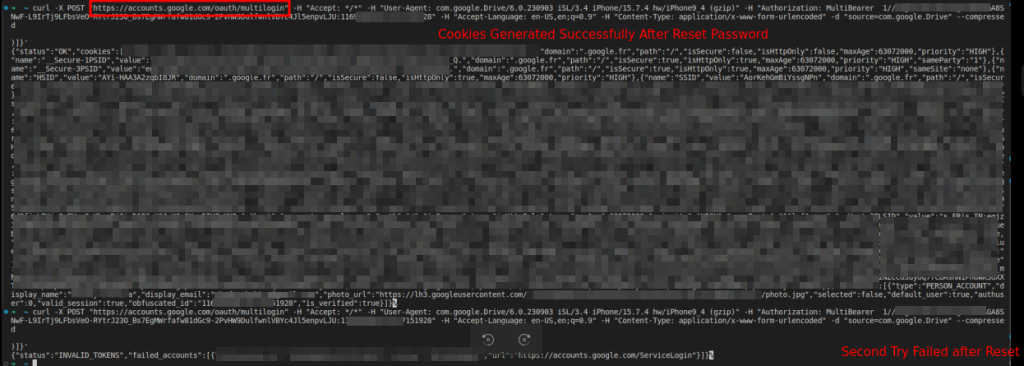
As revealed in Chromium’s source code, the MultiLogin endpoint works by accepting a vector of account IDs and authentication login tokens, which are essential for managing concurrent sessions and seamlessly switching between user profiles.
Investigation of the Chromium codebase confirms that while the MultiLogin feature plays an important role in user authentication, it can be exploited if mishandled. Threat actors are employing sophisticated tactics in cyberthreats, such as Lumma’s undocumented exploitation of Google OAuth2 MultiLogin endpoints.
Lumma’s approach involves working with key components: token and GAIA ID pairs. Google authentication process. By applying encryption to this component, Lumma effectively masks the core mechanism of the exploit and prevents other malicious entities from replicating its techniques. This strategic move maintains the uniqueness of the exploit in a competitive cybercrime environment and gives it an edge in the illicit market.
Subsequent adaptations of Lumma include using SOCKS proxies to circumvent Google’s IP-based restrictions on cookie regeneration, which inadvertently exposes some request and response details, making it vulnerable to exploits. Concealability may be compromised. Encrypted communication between the malware C2 and the MultiLogin endpoint is less likely to trigger alarms in network security systems because standard security protocols typically overlook encrypted traffic.
This exploit could continuously regenerate cookies for Google services, and signals a shift toward more sophistication and stealth orientation of Google’s internal authentication mechanisms. cyber threatsemphasizes concealment over effectiveness.
Related article
- Scammers weaponize Google Forms in new BazarCall attacks
- Google Workspace vulnerability leads to network-wide compromise
- Hackers steal $59 million in crypto via malicious Google and X ads
- Google’s Latest Android Feature Drops: Dark Web Search for Gmail IDs
- Fantom Foundation falls victim to wallet hacking due to zero-day flaw in Google Chrome