Unspecified government entities in Afghanistan were targeted by a previously undocumented web shell. HRServ This attack appears to be an Advanced Persistent Threat (APT) attack.
The web shell, a dynamic link library (DLL) named hrserv.dll, has “advanced features such as custom encoding schemes for client communication and in-memory execution” (Kaspersky security researcher Mert Mr. Degirmenci) Said In an analysis published this week.
A Russian cybersecurity company announced that it had identified a malware variant dating back to early 2021 based on the compilation timestamps of these artifacts.
Web shells are typically malicious tool Provides remote control of compromised servers. Once uploaded, the attacker can perform a variety of post-exploitation activities, including stealing data, monitoring servers, and advancing laterally within the network.
The attack chain includes: PAExec Alternative remote management tools PsExec It is used as a launchpad to create a scheduled task disguised as a Microsoft update (‘MicrosoftsUpdate’), which is then configured to run a Windows batch script (‘JKNLA.bat’).
The batch script takes the absolute path to the DLL file (‘hrserv.dll’) as an argument. This file runs as a service that starts an HTTP server that can parse incoming HTTP requests for subsequent actions.
“Based on the type and information within the HTTP request, certain features are activated,” Degirmenci said, adding that “the GET parameters used in the hrserv.dll file used to mimic Google services “contains ‘hl’,” he added.
This may be an attempt by the attacker to mix these malformed requests into network traffic, making it more difficult to distinguish between malicious activity and benign events.
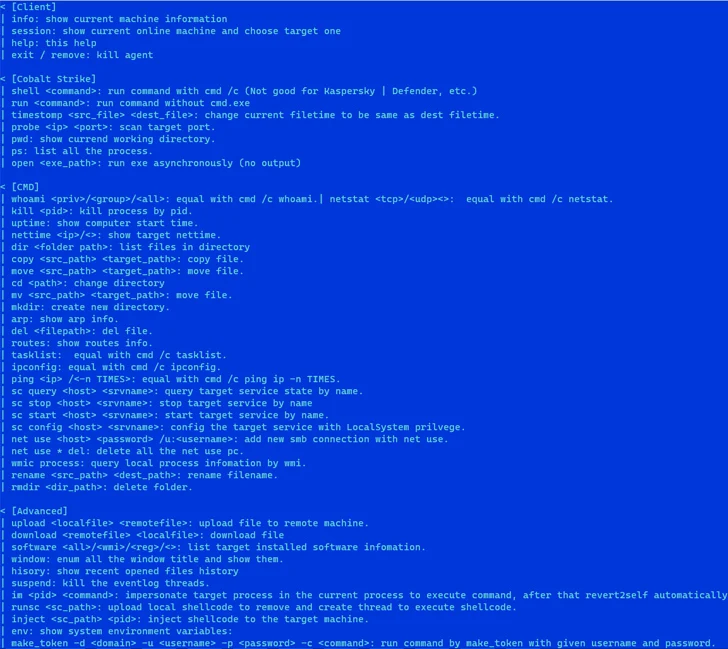
These HTTP GET and POST requests have an embedded parameter called cp whose value (0-7) determines the next action. This includes spawning new threads, creating files with arbitrary data written to them, reading files, and accessing files. Outlook web app HTML data.
If the value of cp in the POST request is equal to ‘6’, code execution is triggered by parsing the encoded data and copying it to memory, after which a new thread is created and the process goes to sleep.
This web shell can also activate the execution of a stealth “multifunctional implant” in memory, which is responsible for erasing forensic traces by removing the “MicrosoftsUpdate” job and initial DLLs and batch files.
The attacker behind the web shell is currently unknown, but several typos in the source code indicate that the malware’s author is not a native English speaker.
“In particular, web shells and memory implants use different strings for certain conditions,” Degirmenci concluded. “Additionally, the memory implant displays a meticulously crafted Help Him message.”
“Given these factors, the malware’s characteristics are more consistent with malicious, financially motivated activity. However, its operational methodology shows similarities to APT behavior.”