A new Go-based malware loader called jinx loader It is used by threat actors to deliver next-level payloads such as Formbook and its successor, XLoader.
of disclosure From cybersecurity companies Palo Alto Networks Unit 42 and Symantec, both highlight a multi-step attack sequence that leads to the deployment of JinxLoader via a phishing attack.
“This malware pays homage to League of Legends characters” jinxfeaturing the character on an advertising poster, [command-and-control] Login Panel”, Symantec Said. “JinxLoader’s main function is simple: load malware.”
unit 42 revealed In late November 2023, the malware service first advertised on the hack forum[.]Available through April 30, 2023, for $60 per month, $120 per year, or $200 for life.
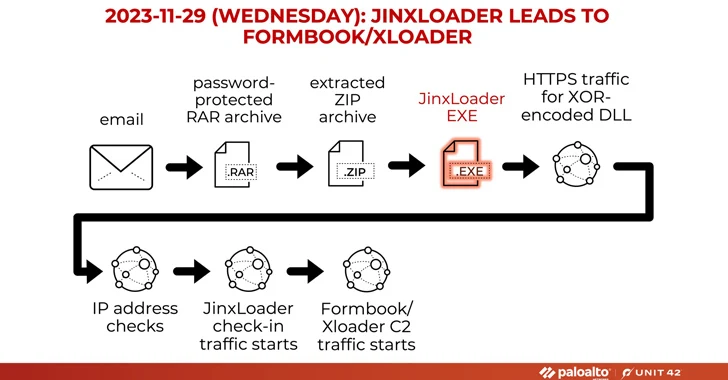
The attack begins with a phishing email impersonating Abu Dhabi National Oil Company (ADNOC) that prompts the recipient to open a password-protected RAR archive attachment. Opening this attachment drops the JinxLoader executable, which then acts as a gateway for Formbook or XLoader.
The development comes after ESET revealed a spike in infections, distributing another novice loader malware family called Rugmi to proliferate a wide range of information thieves.
It also comes amid a surge in campaigns distributing DarkGate and PikaBot by a threat actor known as TA544 (also known as Narwal Spider). use A new variant of loader malware called IDAT Loader for deploying Remcos RAT or SystemBC malware.
Furthermore, the threat actors behind Meduza Stealer are released An updated version (version 2.2) of the malware on the dark web expands support for browser-based cryptocurrency wallets and improves credit card (CC) grabbers.
In a sign that stealer malware continues to be a lucrative market for cybercriminals, researchers have discovered a new malware known as Vortex Stealer that can steal browser data, Discord tokens, Telegram sessions, system information, and files smaller than 2 MB. I discovered the Steeler family. In terms of size.
“Stolen information is archived and uploaded to Gofile or Anonfiles. The malware also posts to the creator’s Discord using webhooks,” Symantec said. Said. “You can also post to Telegram via the Telegram bot.”