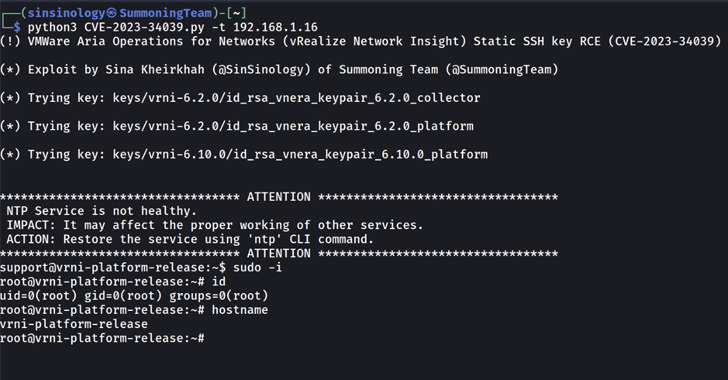
Proof-of-concept (PoC) exploit code is now available for a recently disclosed and patched critical flaw affecting VMware Aria Operations for Networks (formerly vRealize Network Insight).
This flaw is tracked as CVE-2023-34039, has a severity rating of 9.8 out of 10, and is described as a case of authentication bypass due to lack of unique cryptographic key generation.
“A malicious attacker with network access to Aria Operations for Networks could bypass SSH authentication and access the Aria Operations for Networks CLI,” VMware announced earlier this week.
Sina Kheirkhah of the Summoning Team, who published the PoC after VMware analyzed the patch, said the root cause can be traced back to a bash script that includes a method called refresh_ssh_keys(). The ubuntu user in the authorized_keys file.
“SSH authentication is in place, but VMware forgot to regenerate the keys,” Kheirkhah said. Said. “VMware’s Aria Operations for Networks had hard-coded keys from version 6.0 to 6.10.”

VMware’s latest fix also addresses CVE-2023-20890, an arbitrary file write vulnerability affecting Aria Operations for Networks. This vulnerability could be exploited by an attacker with administrative access to write files to arbitrary locations, resulting in remote code execution.
In short, an attacker could leverage a PoC to gain administrative access to a device and exploit CVE-2023-20890 to execute arbitrary payloads, so to protect against potential threats, It is important that users apply the updates.
The PoC release comes as the virtualization technology giant issues a fix for a high severity SAML token signing bypass flaw (CVE-2023-20900, CVSS score: 7.5) across several Windows and Linux versions of VMware Tools. It was done at the same time.
“A malicious attacker who deploys a man-in-the-middle (MITM) network within a virtual machine network could bypass SAML token signature validation and perform VMware Tools guest operations,” the company said. I am. Said In an advisory released Thursday.
Peter Stöckli of GitHub Security Lab is credited with reporting this flaw, which affects the following versions:
- VMware Tools for Windows (12.xx, 11.xx, 10.3.x) – Fixed in 12.3.0
- VMware Tools for Linux (10.3.x) – fixed in 10.3.26
- Open source implementation of VMware Tools for Linux or open-vm-tools (12.xx, 11.xx, 10.3.x) – Fixed in 12.3.0 (to be distributed by Linux vendor)
This development comes after Fortinet FortiGuard Labs warned that vulnerabilities in Adobe ColdFusion are being continuously exploited by threat actors to deploy cryptocurrency miners. hybrid bot It has the ability to perform cryptojacking and distributed denial of service (DDoS) attacks, such as Satan DDoS (aka Lucifer) and RudeMiner (aka SpreadMiner).
A backdoor named bill gates (alias Setag) is known for hijacking systems, stealing sensitive information, and launching DDoS attacks.